In the past we have been cautious to keep our smart phone clear of any key stroke logger or a cell phone monitoring software in order to keep our personal information safe. However the latest Android threat is not interested in stealing your information rather it is out to destroy it and cause as much damage as possible.
Regular anti keystroke logger precautions and security apps which help to filter out cell phone monitoring capable software are no good here as this virus is not bundled with an app as many other Android pests are. Rather this virus can be triggered simply by visiting a compromised web site.
Smart phone security experts demonstrated at the Ekoparty security conference exactly how the virus works. By deploying a unique factory reset code within the iFrame of a given Uniform Resource Identifier (URI) the virus can exploit a visitor’s device. As users visit the web page from their smart phone, while the page is loaded the code is also being executed and the device from which the page was visited undergoes a factory reset. Upon testing which devices are vulnerable to this new security threat it was found that nearly all of Samsung’s new devices can fall prey to it, together with a number of new Android devices from other manufacturers.
Upon further analysis of how this virus can spread it was uncovered that the hacker can forward the link in an SMS message or email and even publish it on to a social network such as Facebook for potential victims to click on and be directed to the page. What’s worse is that the attacker can also force a device to visit the web link and have it reset itself through the Near Field Communication (NFC) technology. By touching a compromised NFC chip with a NFC enabled device it is possible to have the device visit the web link automatically. Furthermore, if the link is attached in a special service message that too will trigger the phone to visit the web page and self reset.
This code exploits a vulnerability which existed in the Android dialer. Through the dialer users are able to input special commands better known as the Unstructured Supplementary Service Data (USSD) codes which allow the user to make use of the services offered by the service provider. USSD codes can be identified easily as they start with the * sign and end with the # character. Other than these there are also Man Machine Interface (MMI) codes which are used in order to access the devices’ own functions.
The MMI codes can also be used to change the SIM cards Personal Identity Number (PIN) however this is done after providing the Personal Unblocking Key (PUK). In the case that the wrong PUK code is repeatedly entered the SIM card will lock itself permanently and the user will have to get a new SIM card issued.
So instead of having the factory reset code in the iFrame the attacker may choose to have ten iFrame’s all loaded with the PIN changing code followed by a random, and most likely, incorrect PUK code. This would render the SIM card in the device which is accessing the web page useless. In addition to this there is still some variation in the PIN changing code among various Android device manufacturers however the PIN changing code is somewhat the same as it is a standardized universal SIM card feature.
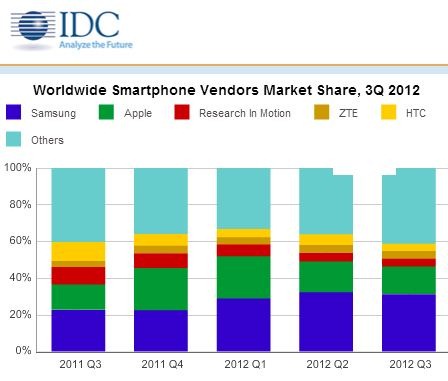
The hardest hit, were devices from Samsung and the firm has quickly made moves to correct this vulnerability in their devices.
[Author Bio: Beth Janick’s work as a web marketer has earned her a dedicated flock of readers who are hankering for the latest news and reviews about best monitoring software for android. Her work revolves around the latest in tech trends like spy apps for android.]





![Cheapest 4G VoLTE Phones under 7000 [Jan 2017]](https://thegadgetfan.com/wp-content/uploads/2016/12/VoLTEphones-190x122.jpg)

